This article has an updated version that you can find here.
With an annual Enterprise license or the EDU Institution license, you are able to use single sign-on (SSO) authentication for both participants and members in order to control access to your Slido organization and to your events.
In this article:
There are two types of SSO protection that you can set up in Slido:
- Participant SSO manages the participants' access. Use Google SSO or SAML based SSO authentication to make sure that only people from your company or specific department can join your internal meetings via Slido.
- Member SSO manages the admin access which allows the members to create and manage Slido events. Only SAML SSO is supported.
Both SSO types are available only in our Enterprise and Institution plans. Participant SSO is also available in our Premium plan. This article will focus on Participant SSO.
Depending on your needs, you can enable both Participant SSO and Member SSO or just one of them. It is also possible to turn off the Participant SSO for a specific event under event settings. This is useful when you want people outside of your organization to participate in some of your events.
Participant SSO
Slido supports the following authentication methods for your event participants:
- Google SSO for participants - If you are using Google Suite at your company, the participants can join your Slido meetings using their Google login credentials.
- SAML based SSO - You can set up SSO protection for your participants with any IdP that supports SAMLv2.0. This article covers all of the most popular identity providers such as Okta, OneLogin, Microsoft Azure or Auth0.
With SSO, your participants can be named or anonymous, depending on the participant privacy setting chosen by the owner
Keep in mind that if you enable Participant SSO for the whole organization, every event will require participants to join via SSO by default. Users can disable this in individual events, unless the account owner locked the setting.
Set up Google SSO for participants
To set up Google SSO for participants:
- Open your Organization settings
- Select Privacy
In the Organization settings, do the following:
- Change your privacy method to Protected
- From the authentication method drop-down menu, select Google SSO
- Enter your company domain
Set up SAML based SSO for participants
To set up SAML based SSO for participants:
- Open your Organization settings
- Select Privacy
In the Organization settings, do the following:
- Change your privacy method to Protected
- From the authentication method drop-down menu, select SAML based SSO
- Upload your metadata file. You can follow these guides to create your .XML file based on your IdP: OneLogin, Okta, Microsoft Azure, Auth0.
Send us a message at support@slido.com if you need any help along the way.
Changing the privacy settings
Only Slido admins and account owners can upload the SAML XML file into the organization settings. Once this is set on the organization level, end-users won’t be able to work with SAML XML file anymore, as it will be automatically propagated from the organization settings.
Apply SAML SSO to all existing events (optional)
Slido admins and account owners can enforce SAML SSO on all events in the organization (including all past and future events) without the exceptions of any individual event, Improving privacy for your organization
SAML SSO configuration details:
Slido authentication process is based on the email as the unique user identifier . Here's the required NameID format:
urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress
Display name is based on the following SAML attributes in this order:
- cn
- displayName
- name
- firstName, lastName (both must be set), e.g. firstName=John and lastName=Doe then display name=John Doe
- email (user part of email address), e.g. john.doe if the email was john.doe@email.com
This information is included in Slido SAML metadata. You can download it directly from Slido admin - Organization settings - Member SAML SSO tab. At the moment, the Organization or Company is not supported as a SAML attribute.
Member SSO
SAML-based single sign-on (SSO) gives Admins, Users, and Guests within a Slido organization access to Slido through their Identity Provider (IdP), for example, Okta, OneLogin, Microsoft Azure, or Auth0, and others.
Member provisioning for selected IdPs is also available. It's possible to leverage our implementation of the SCIM protocol in case the IdP adheres to SCIM standards.
Member SSO can only be set up by the owner of the Slido organization.
Steps to set up member SSO:
- Upload your Identity Provider’s SAML metadata XML file to Slido
- Test the configuration
- Enable SSO
- Enforce your members to log in via SSO
- Allow Guests to log in without SAML SSO
- Set up Member provisioning in selected Identity Providers
Upload your IdP's SAML metadata XML file to Slido
To get started, you need to set up your Identity Provider and acquire its SAML metadata XML file. Once you have it, you can upload it to your Slido organization.
- Open Organization settings
- Select Member SAML SSO
- Click Browse files to upload your IdP's SAML metadata XML file
Once uploaded, our system validates the XML file.
If the file is correct, you will see the Entity ID of your IdP updated. You may then continue with the setup.
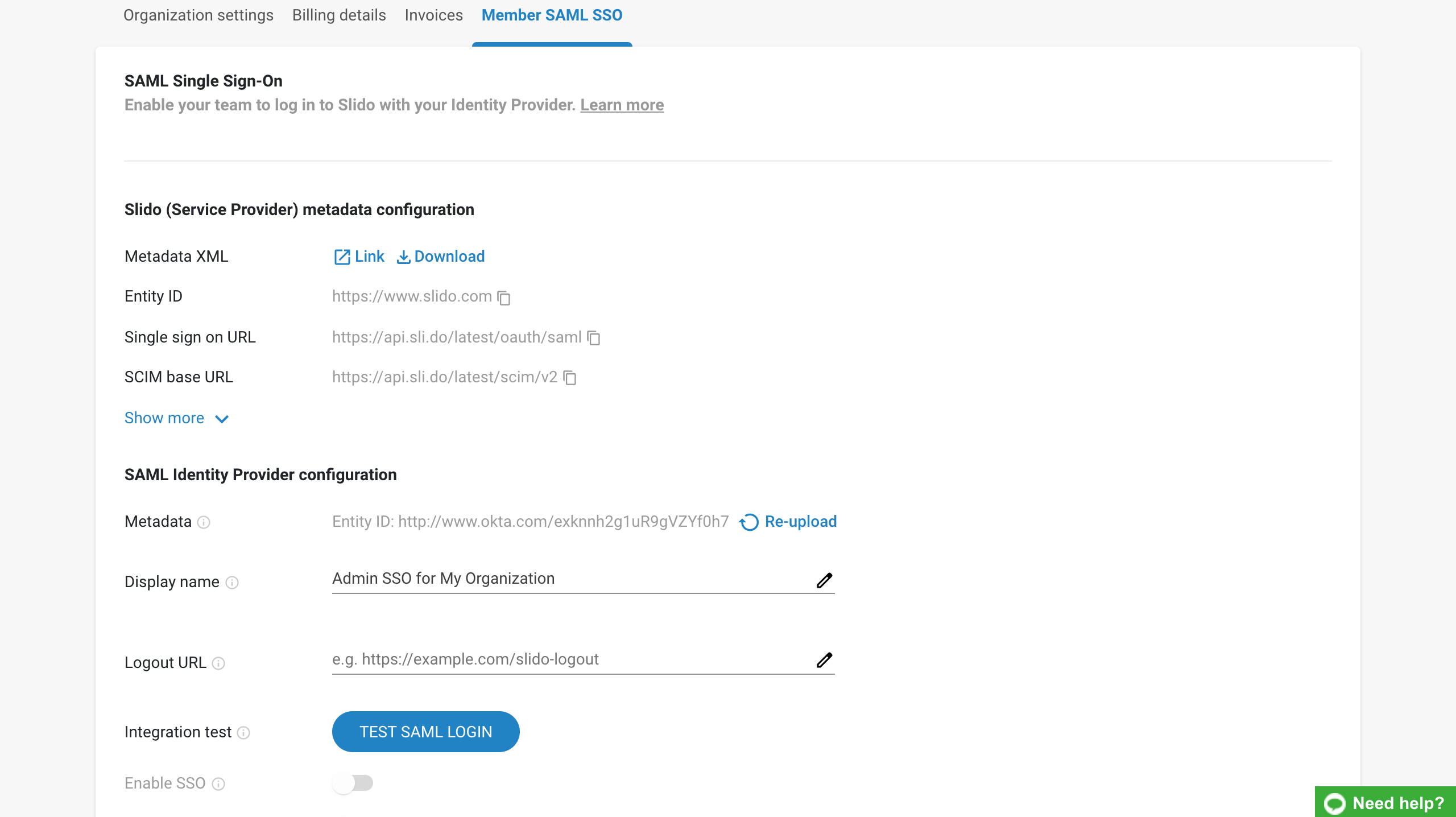
Test the configuration
Before enabling the configuration, you first have to test it by clicking Test SAML Login.
This opens a new window redirecting you to your Identity Provider in order to validate that the integration setup is correct on both sides.
Successful test
If the integration is correctly set up and the test is successfully completed you will see a message saying Test successfully completed. Click Got it to go back to your Organization settings to continue with the setup.
Unsuccessful test
If the integration test fails you will see a message saying Test failed. Click Back to to go your Organization settings to fix the issue.
If the test fails, please double-check the uploaded XML metadata file. Also make sure that the person setting up the authentication in Slido is assigned to the associated SAML SSO application on the IdP side.
Enable SSO
After a successful test, you can enable the integration by clicking the Enable SSO button.
How it works for your members:
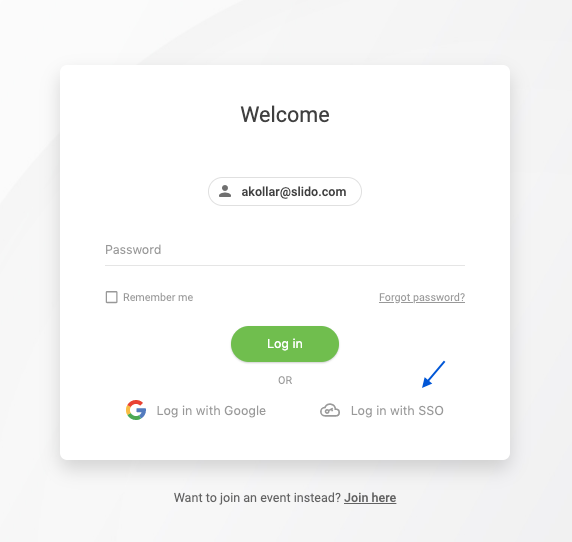
Once Member SSO is enabled, your members will be able to log in to Slido using SSO.
The member's other login options (such as password or Google login) will still remain available as well. The screenshot below shows the experience of a member who has the option to log in using either password or SAML SSO integration.
Once the user chooses to Log in with SSO, they will automatically be redirected to your Identity Provider.
Enforce your members to log in via SSO
When Member SAML SSO is enabled, you may choose to enforce it by clicking the Enforce SSO button. Enforced SSO means that it is mandatory for members to log in using your Identity Provider. This helps to fully secure your organization account.
How it works for your members:
If the SAML SSO is enforced, any member trying to log in will have to go through your IdP's authentication. The members will no longer have the option to log in with with Slido password or Google SSO. Instead, they will be redirected to your IdP.
Once you enforce SAML SSO, the members who are logged in at that moment will have to re-login to their Slido account.
Allow Guests to log in without SAML SSO
By default, when SSO is set up for the organization, the members can only invite other existing members to their events as guests. Sometimes, it might be useful to invite guests who are not from your company.
To allow inviting guests who are not a part of your Slido organization:
- Open Organization Settings - Member SAML/SSO
- Tick the Exclude guests option
The invited guests who are not part of your organization will use a password or Google account to log in to Slido.
Set up Member provisioning in selected Identity Providers
You can set up SAML SSO and provisioning for your Slido organization in the following IdP's, or any other that complies with SCIM standards:
- Okta
- OneLogin
- Microsoft Azure
- Auth0
Useful information and FAQ:
- Does Slido SSO authentication work from the service provider side, IdP, or both?
Slido supports both SSO authentication flows.
- How do I renew the SSO certificate?
To renew your SSO certificate in Slido you will first need to disable member SSO in Organization settings. This will log you out so you need to log back in, open Organization settings and select Re-upload which you can find next to Metadata. Now upload your new .xml file, click Test SAML Login and if the test is successful, enable SSO again.
Take a look at our video tutorial for renewing the SSO certificate
- Can we use the same SAML XML file for both - participant and member SSO?
Yes, this is possible. Be careful with using the single file setup with user provisioning though - the participants don't create accounts the same way as Slido organization members. User provisioning won't work correctly if you mark the participants and the members for provisioning the same way. A 2-app setup on the IdP side is recommended. Please contact us at support@slido.com if you need any help with your user provisioning setup.
- Can I test the member SSO before saving the settings to make sure it's working?
There is no testing environment for the member SSO setup at the moment, but there is a test as a part of the setup process. If the test passes it means the integration is working well and member SSO can be enforced for your Slido organization. That should be sufficient to validate your setup before it's applied to your Slido organization.
- Can participants still ask questions anonymously when there is SSO set up for the event?
Yes! This helps to keep your data Private without any compromise on the level of the audience engagement.
- We usually use Slido at the internal meetings, but there will be participants from outside of our company at the upcoming event. Will be they able to engage via Slido?
Sure! You can disable the SSO login for the specific event in Event Settings - Privacy - Require authentication - Google/SAML SSO.

